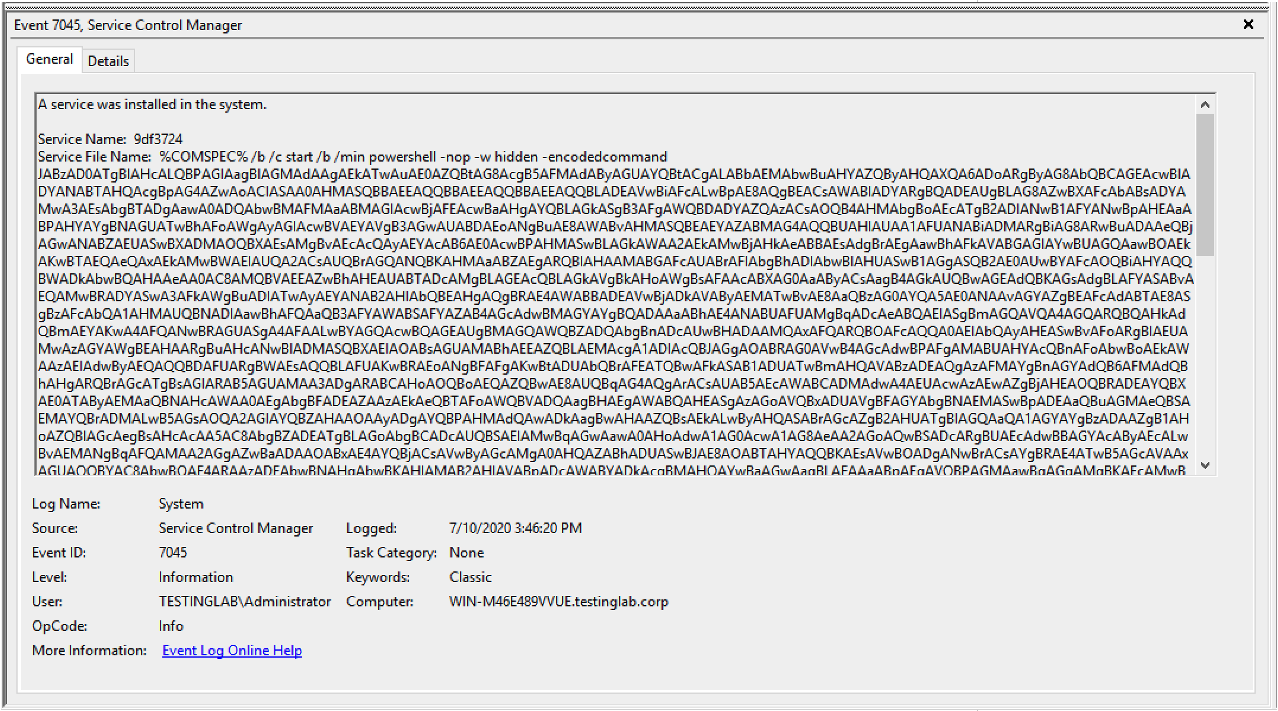
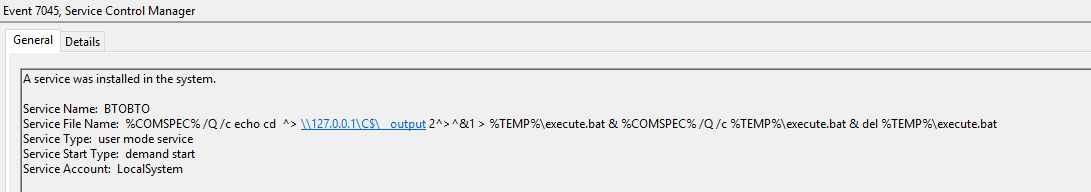
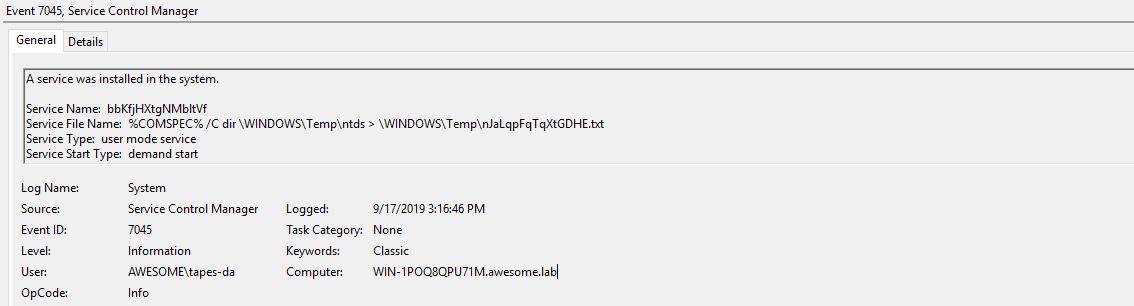
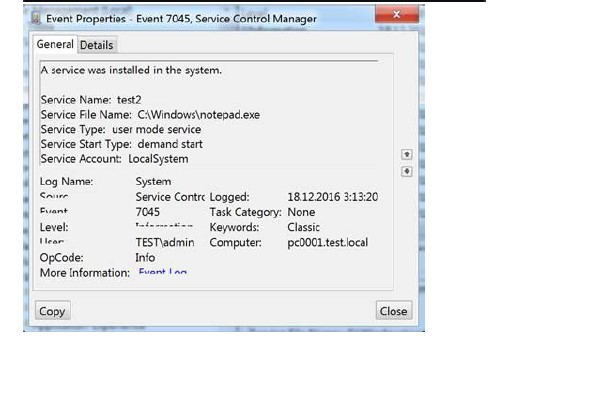
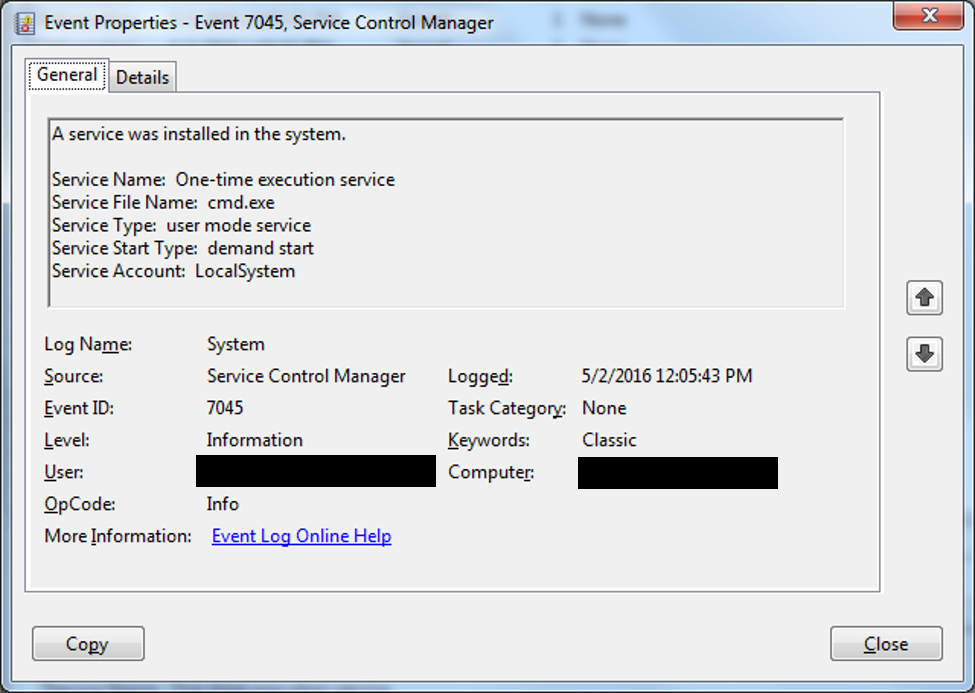
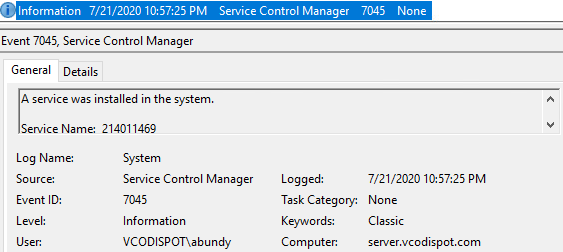
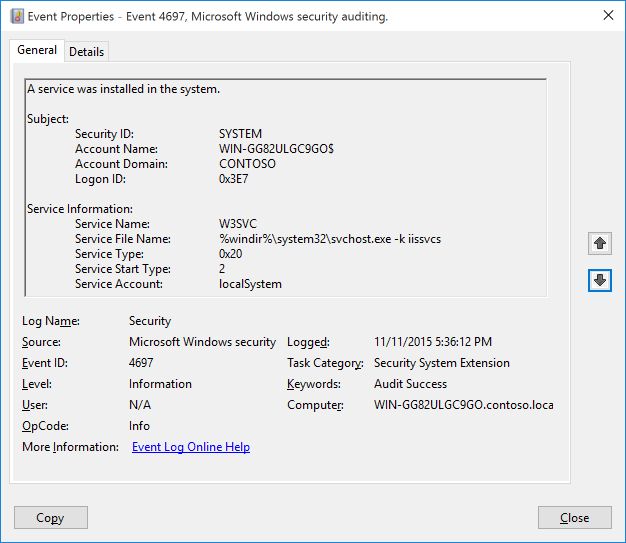
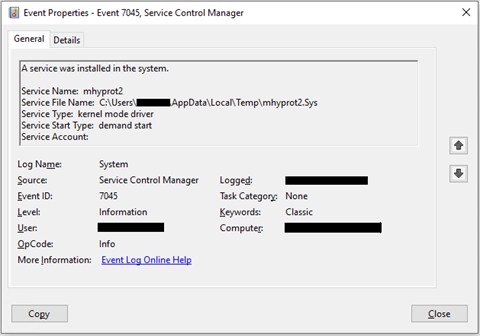
From the Shadows to the Light: Exposing Red Team Attacks through Windows Event Logs | by Umar Ahmed | Medium

Qbot and Zerologon Lead To Full Domain Compromise - Malware News - Malware Analysis, News and Indicators
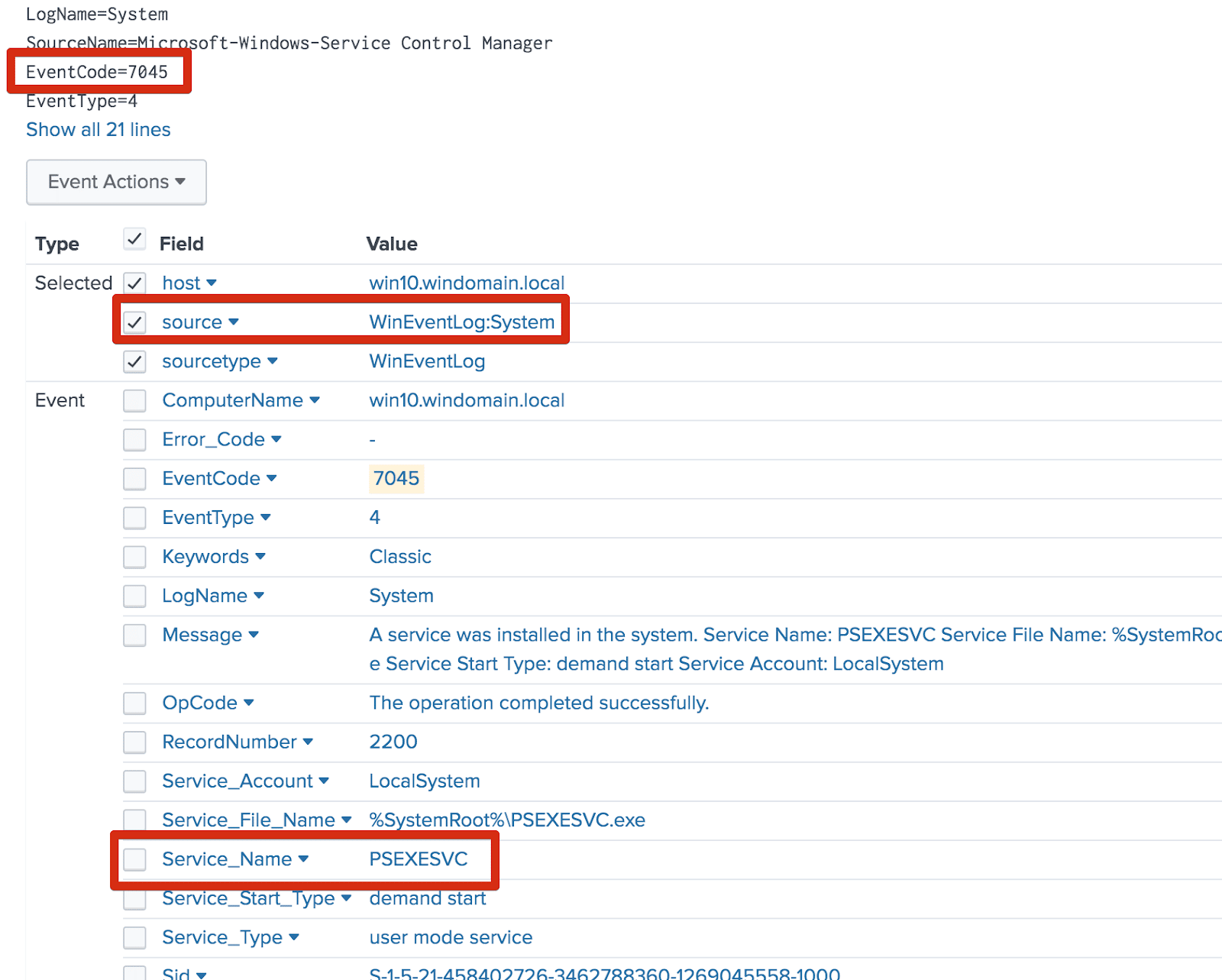
![Kostas on X: "🎯Detecting/Hunting PsMapExec Default Values (Two of the most commonly seen methods) 1️⃣SMB Method: Service Creation - EIDs 7045(System) and 4697(Security) - Service name regex: 'Service_[a-z]{16}' - Service File name: Kostas on X: "🎯Detecting/Hunting PsMapExec Default Values (Two of the most commonly seen methods) 1️⃣SMB Method: Service Creation - EIDs 7045(System) and 4697(Security) - Service name regex: 'Service_[a-z]{16}' - Service File name:](https://pbs.twimg.com/media/F_IKAVSa8AA4TCy?format=jpg&name=large)
Kostas on X: "🎯Detecting/Hunting PsMapExec Default Values (Two of the most commonly seen methods) 1️⃣SMB Method: Service Creation - EIDs 7045(System) and 4697(Security) - Service name regex: 'Service_[a-z]{16}' - Service File name:
![c# - Windows could not start the [service name] service on Local Computer. Error 5: Access is Denied - Stack Overflow c# - Windows could not start the [service name] service on Local Computer. Error 5: Access is Denied - Stack Overflow](https://i.stack.imgur.com/5uRHt.png)
c# - Windows could not start the [service name] service on Local Computer. Error 5: Access is Denied - Stack Overflow

Service does not run on Windows 2019 - FDB Snapshot 20200510 · Issue #10 · evolvedbinary/fusiondb-server · GitHub



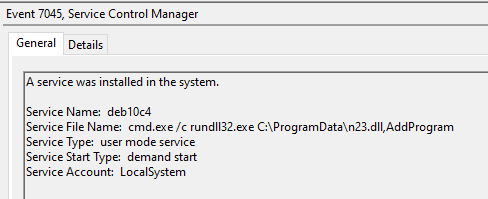



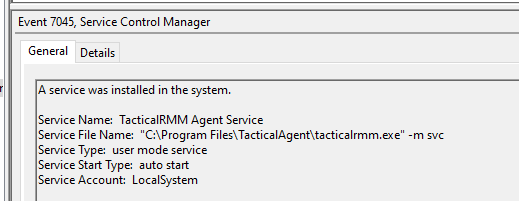
![Event ID 7045: A Service was Installed in the System [Fix] Event ID 7045: A Service was Installed in the System [Fix]](https://windowsreport.com/wp-content/uploads/2023/06/event-id-7045.png)