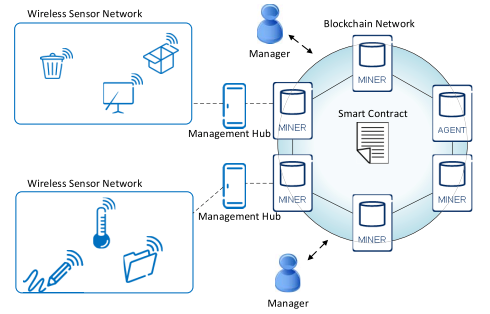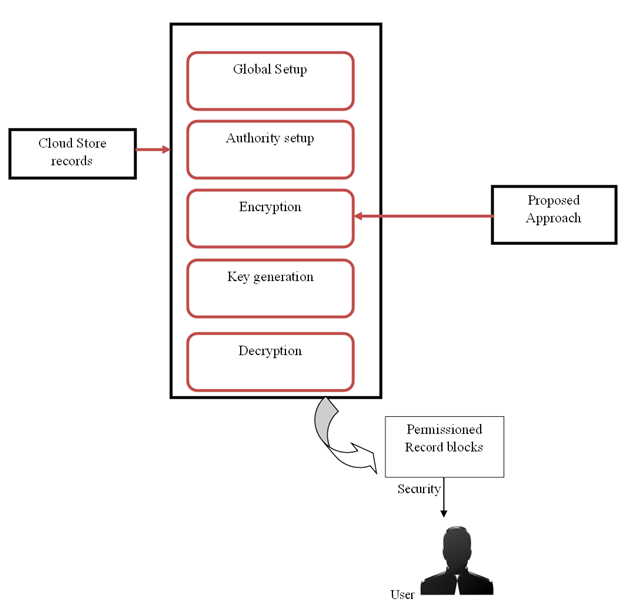
Securing IoT system Access Control using Blockchain-Based Approach | International Journal of Intelligent Systems and Applications in Engineering
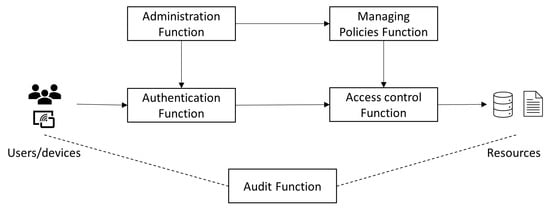
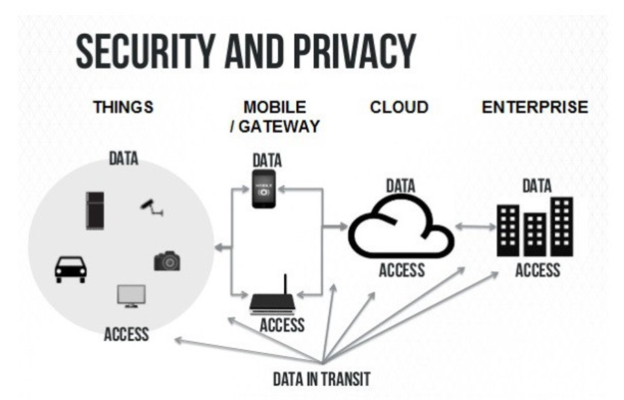
Sensors | Free Full-Text | Access Control for IoT: A Survey of Existing Research, Dynamic Policies and Future Directions

Distributed access control solution for the IoT based on multi-endorsed attributes and smart contracts | Semantic Scholar


![PDF] Security , Privacy & Trust in Internet of Things : the road ahead | Semantic Scholar PDF] Security , Privacy & Trust in Internet of Things : the road ahead | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a7883e5848fde68041dc150d0d36641d921b8ee9/3-Figure1-1.png)